Digital forensic imaging for law enforcement and corporate investigations The increasing diversity, size and sophistication…
Cellebrite Inspector
Analice las 4 plataformas principales con 1 herramienta
Adquiera un snapshot rápidamente
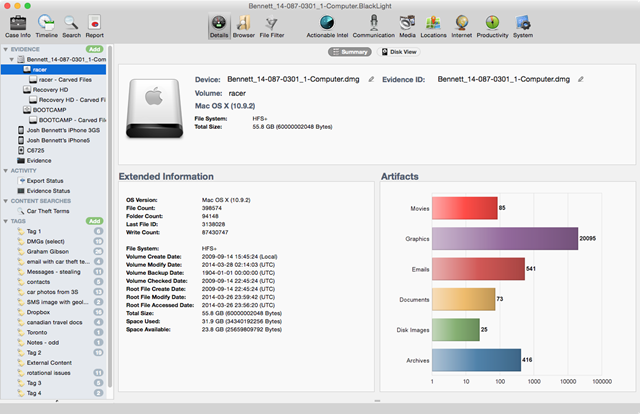
Adquiera rápidamente una instantánea del dispositivo del usuario. La vista Detalles de BlackLight proporciona una visualización de las configuraciones y el uso de cada dispositivo incluido en su archivo de caso, incluyendo:
- Tipo de dispositivo, versión del sistema operativo, número de serie, UDID e IMEI.
- Estadísticas de resumen de artefactos para documentos, correos electrónicos, películas, llamadas, correo de voz y más.
- Información de la cuenta del usuario del dispositivo y la información habitual de las cuentas de Internet para aplicaciones como Twitter e iCloud.
- Historial de uso reciente, incluyendo números de teléfono marcados (con la información de contacto asociada), últimas aplicaciones ejecutadas y las búsquedas web de localización más recientes.
Descubra fácilmente las acciones del usuario
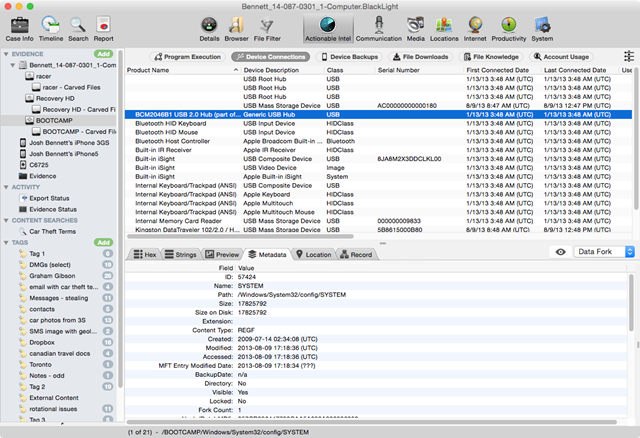
La innovadora vista Actionable Intel de BlackLight permite a los examinadores ver varios puntos de datos que pueden atribuirse a las acciones de un usuario. Se recogen y organizan rastros de la actividad potencialmente importante del usuario desde muchos lugares dispares para un examen práctico y eficiente. Los elementos incluyen:
- Archivos y programas recientemente ejecutados, extraídos del Registro de Windows, archivos de enlaces, jumplists, Prefetch y Superfetch.
- Datos de conexión de todos los dispositivos previamente conectados al sistema, incluyendo las fechas/horas de conexión de los dispositivos USB y la cuenta de usuario asociada.
- Copias de seguridad de los dispositivos iOS.
- Descargas recientes de archivos.
- Papelera (para los volúmenes de Mac OS X) y Papelera de reciclaje (para los volúmenes de Windows).
Información actual y eliminada de la cuenta de usuario.
Examine con rapidez grandes conjuntos de datos
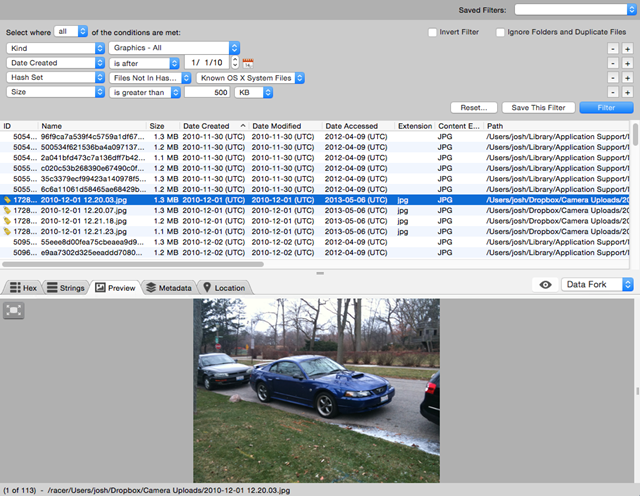
La vista Filtro de Archivos de BlackLight incluye opciones de filtro definidas por el examinador para localizar rápidamente los datos relevantes dentro de grandes conjuntos de datos. Los criterios de filtro incluyen:
- Nombre, tipo, tamaño o extensión del archivo.
- Fecha de creación, modificación o acceso.
- Metadatos de imagen, incluyendo las coordenadas GPS y el tipo de cámara (dispositivo iOS).
- Filtrado de conjuntos de hash positivos y negativos.
Los examinadores pueden aplicar cualquier número de filtros o filtros inversos para separar con rapidez los datos importantes de los archivos de sistema y archivos de aplicación. BlackLight viene con varios filtros de archivo predefinidos, incluyendo aquellos que filtran por tipo de archivo, atributo de archivo, coordenadas de geolocalización y tipo de dispositivo fuente.
Encuentre las pruebas de imagen y video que necesita
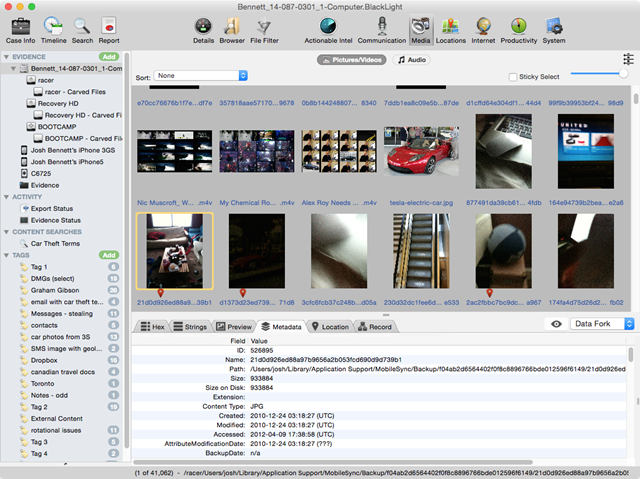
La vista Media de BlackLight tiene incorporado el soporte para todos los tipos de archivos de imagen y video comúnmente utilizados, e incluye varias características de análisis útiles y orientadas al examinador, tales como:
- Cartografía (mapping) GPS incorporada:
- Todos los archivos de medios que contengan datos GPS serán identificados con un icono de marca de lugar.
- Los examinadores pueden ver los datos de geolocalización de los archivos de medios en un mapa Mercator (sin conexión) o utilizando Google Maps (en línea) directamente desde la vista GPS incorporada.
- Algoritmo propio de análisis del tono de piel:
- Ordena los archivos de imagen y video por el porcentaje de tono de piel contenido en el archivo.
- Análisis de fotogramas (frames) de vídeo:
- BlackLight inicialmente muestra los archivos de video como secuencias de frames 4×4 , permitiendo a los examinadores revisar rápidamente múltiples archivos de video para localizar posibles pruebas.
Recupere todos los mensajes de las fuentes más comunes
La vista Comunicación de BlackLight permite a los examinadores ver un registro completo de llamadas, correo de voz, actividad en redes sociales y más. Lo que es más importante, los examinadores pueden ver los hilos de mensajes en la vista de lista o en su formato nativo, con soporte para datos de:
- Servicios de texto
- SMS / MMS
- iMessage
- iChat
- Aplicaciones de mensajería
- Skype
- Kik
- TextPlus
- TextFree
- Redes sociales
- Foursquare
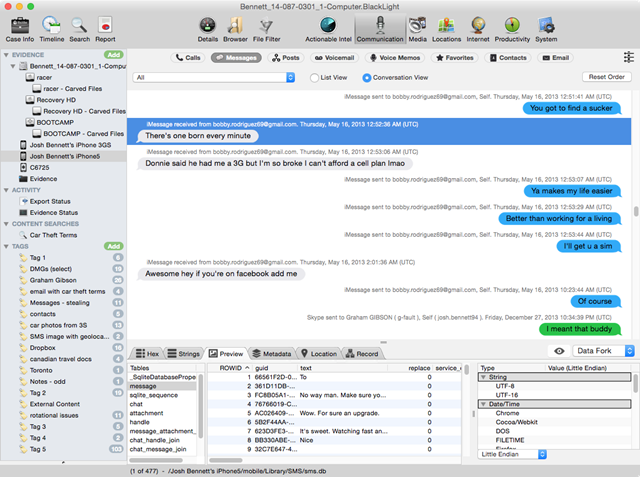
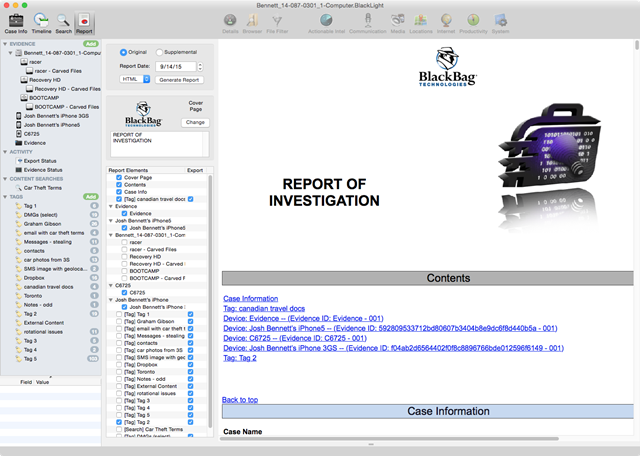
Personalice su informe
BlackLight está diseñado para que crear informes sea increíblemente flexible. Los examinadores pueden exportar grandes conjuntos de datos en un formato fácil de leer, y pueden exportar informes en una variedad de formatos para permitir el intercambio fácil de información con todas las partes interesadas. Con la vista Informe de BlackLight, puede:
- Etiquetar fácilmente la evidencia e incluir todos los metadatos relevantes en el informe del examinador.
- Exportar su informe en los formatos que elija, incluidos
- .html
- .docx
- .TXT
- Exportar datos de eDiscovery a un archivo genérico de carga Concordance, compatible con las principales plataformas de revisión.
- Enmascarar (blur) los datos confidenciales contenidos en los informes del examinador que se vayan a compartir con terceros no autorizados.