Con Fivecast MATRIX ayudamos a las agencias y organizaciones gubernamentales a abordar los retos inherentes a los enormes volúmenes de verificación de personas para un abanico de casos de uso de misión crítica.

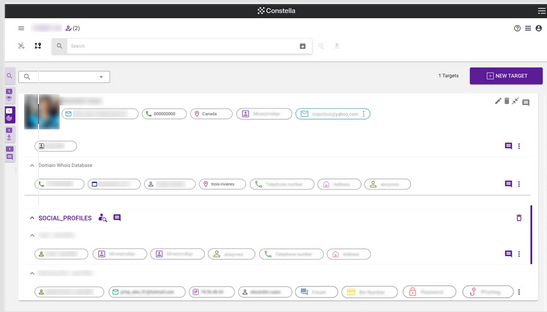
Constella Intelligence Hunter
Hunter for Fraud Investigations: efficient, targeted, intuitive investigations
A platform designed to improve the fraud investigation process to make it easier and quicker to stay ahead of threat actors and unmask attackers by helping users efficiently attribute identities and identify further intelligence across multiple data sources simultaneously to expose the true identity of threat actors.
Simple, tergeted threat analysis and search
Empower users to simply start with an attribute search and pivot, enriching information, making correlations across data sources and collating intelligence in one place. Search multiple attributes at once with our bulk search feature.
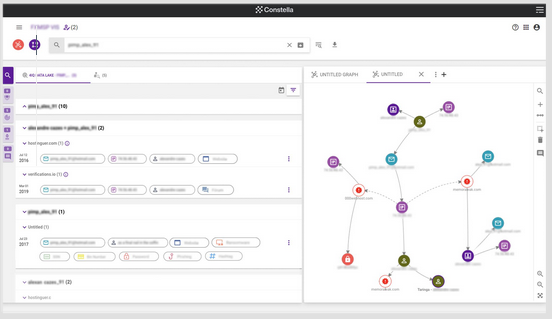
Comprehensive, intuitive visualizations
Visualize collected data in a dedicated, controlled workspace to easily identify links and conduct network analysis for a complete investigative picture—incorporating multiple sources and manual entries, downloading, saving and uploading, as needed.
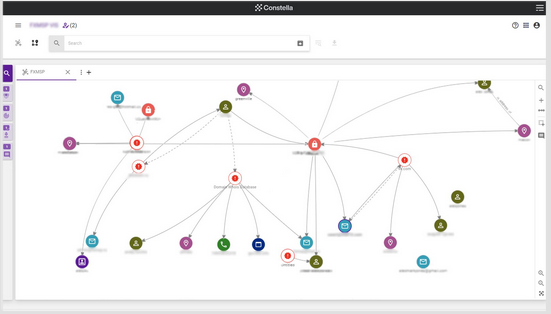
Automated data correlations and target packs
Save time and resources by producing actor summaries through automated breach data correlations, and build comprehensive profiles by recording targeted intelligence in dedicated target areas.
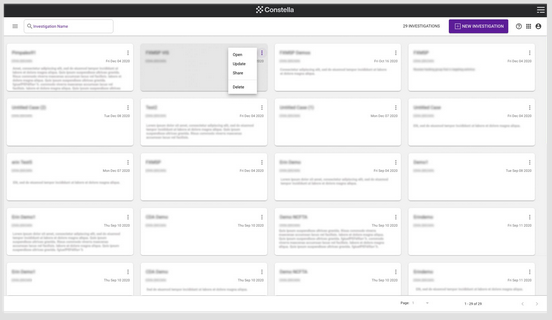
Fluid investigation management
Create multiple investigations and share with colleagues for collaborative working—building case-specific results, graphs, target packs, notes—archiving for future access or auditing—and deleting when no longer needed.
Password pivoting
Improve real identification by identifying additional accounts using passwords collected from breaches.
Malicious scores
Use ML-produced scoring of entities associated with malicious breaches to gain context into how malicious search terms might be.
Total privacy
Completely protect searches from outside detection using our proprietary encryption methods—not even our teams can view which searches are conducted.
Configuration
Configure the platform to provide proxies to obfuscate your investigations, and use strong audit capabilities to monitor what searches are conducted.